Use specific directory servers as the LDAP server
Overview
For a list of supported LDAP servers, refer to the Supported hardware and software Web site.
Support is limited to directory servers that follow the LDAP specification. You can any other directory server by using the custom directory type in the list and by filling in the required filters.
To improve performance for LDAP searches, the default filters for IBM Tivoli Directory Server, Sun ONE, and Active Directory are defined such that when you search for a user, the result contains all the relevant information about the user (user ID, groups, and so on). As a result, WAS does not call the LDAP server multiple times. This definition is possible only in these directory types, which support searches where the complete user information is obtained.
Microsoft Active Directory forests are not supported with the standalone or federated LDAPs.
Using IBM Tivoli Directory Server as the LDAP server
To use IBM Tivoli Directory Server, formerly IBM Directory Server, select IBM Tivoli Directory Server as the directory type.
With TDS, group membership is an operational attribute and lookup for all group memberships, including static, dynamic, and nested, is done by enumerating the ibm-allGroups attribute for the entry.
For IBM Directory Server, select option...
-
Ignore case for authorization
This is required because when the group information is obtained from the user object attributes, the case is not the same as when you get the group information directly. For authorization to work, perform a case insensitive check.
For Tivoli Directory Server, use a case-insensitive match so that attribute values returned by the ibm-allGroups attribute are all in uppercase.
To avoid port conflicts, IBM recommends not installing TDSv6.0 on the same machine that you install WAS v7.0. TDS v6.0 includes WAS Express v5.1.1, which it uses for an admin console. Install the Web Administration tool v6.0 and WAS Express v 5.1.1, which are both bundled with TDS v6.0, on a different machine from WAS v7.0. You cannot use the WAS v7.0 admin console for TDS.
If install TDSv 6.0 and WAS v7.0 on the same machine...
- During the TDS installation process, select both the Web Administration tool and WAS Expressv 5.1.1.
- Install WASv7.0.
- When you install WASv7.0, change the port number for the appserver.
- You might need to adjust the WAS environment variables on WASv7.0 for...
- WAS_HOME
- WAS_INSTALL_ROOT
- APP_ROOT (IBM i)
To change the variables using the admin console, click...
-
Environment | WebSpherevariables
Use a Lotus Domino Enterprise Server as the LDAP server
If we select the Lotus Domino Enterprise Serverv6.5.4 or v7.0 and the attribute short name is not defined in the schema, we can take either of the following actions:- Change the schema to add the short name attribute.
- Change the user ID map filter to replace the short name with any other defined attribute (preferably to UID). For example, change person:shortname to person:uid.
The userID map filter is changed to use the uid attribute instead of the shortname attribute as the current version of Lotus Domino does not create the shortname attribute by default. To use the shortname attribute, define the attribute in the schema and change the userID map filter.
User ID Map : person:shortname
Use Sun ONE Directory Server as the LDAP server
You can select Sun ONE Directory Server for the Sun ONE Directory Server system. In Sun ONE Directory Server, the object class is the default groupOfUniqueName when creating a group. For better performance, WAS uses the User object to locate the user group membership from the nsRole attribute. Create the group from the role. To use the groupOfUniqueName attribute to search groups, specify our own filter setting. Roles unify entries. Roles are designed to be more efficient and easier to use for applications. For example, an application can locate the role of an entry by enumerating all the roles that are possessed by a given entry, rather than selecting a group and browsing through the members list. When using roles, we can create a group using a:
- Managed role
- Filtered role
- Nested role
All of these roles are computable by the nsRole attribute.
Use Microsoft Active Directory server as the LDAP server
To use Microsoft Active Directory as the LDAP server for authentication with WAS take specific steps. By default, Microsoft Active Directory does not permit anonymous LDAP queries. To create LDAP queries or to browse the directory, an LDAP client must bind to the LDAP server using the distinguished name (DN) of an account that has the authority to search and read the values of LDAP attributes, such as user and group information, needed by the appserver. A group membership search in the Active Directory is done by enumerating the memberof attribute for a given user entry, rather than browsing through the member list in each group. If we change the default behavior to browse each group, we can change the Group Member ID Map field from memberof:member to group:member.
The following steps describe how to set up Microsoft Active Directory as the LDAP server.
- Determine the full distinguished name (DN) and password of an account in the administrators group. For example, if the Active Directory administrator creates an account in the Users folder of the Active Directory Users and Computers Windows control panel and the DNS domain is ibm.com, the resulting DN has the following structure:
cn=<adminUsername>, cn=users, dc=ibm, dc=com
- Determine the short name and password of any account in the Microsoft Active Directory.
- Use the WAS admin console to set up the information that is needed to use Microsoft Active Directory.
- Click...
- Security | Global security
- Under User account repository, select Standalone LDAP registry and click Configure.
- Set up LDAP with Active Directory as the type of LDAP server. Based on the information that is determined in the previous steps, we can specify the following values on the LDAP settings panel:
- Primary administrative user name
- Specify the name of a user with admin privileges that is defined in the registry. This user name is used to access the admin console or used by wsadmin.
- Type
- Specify Active Directory
- Host
- Domain name service (DNS) name of the machine that is running Microsoft Active Directory.
- Base distinguished name (DN)
- Domain components of the DN of the account that is chosen in the first step. For example: dc=ibm, dc=com
- Bind distinguished name (DN)
- Full distinguished name of the account that is chosen in the first step. For example: cn=adminUsername, cn=users, dc=ibm, dc=com
- Bind password
- Password of the account that is chosen in the first step.
- Click OK and Save to save the changes to the master configuration.
- Click...
- Click...
- Security | Global security
- Under User account repository, click the Available realm definitions drop-down list, select...
- Standalone LDAP registry | Configure
- Select either the Automatically generated server identity or Server identity that is stored in the repository option. If we select the Server identity that is stored in the repository option, enter the following information:
- Server user ID or admin user on av6.0.x node
- Specify the short name of the account that is chosen in the second step.
- Server user password
- Specify the password of the account that is chosen in the second step.
- Set ObjectCategory as the filter in the Group member ID map field to improve LDAP performance.
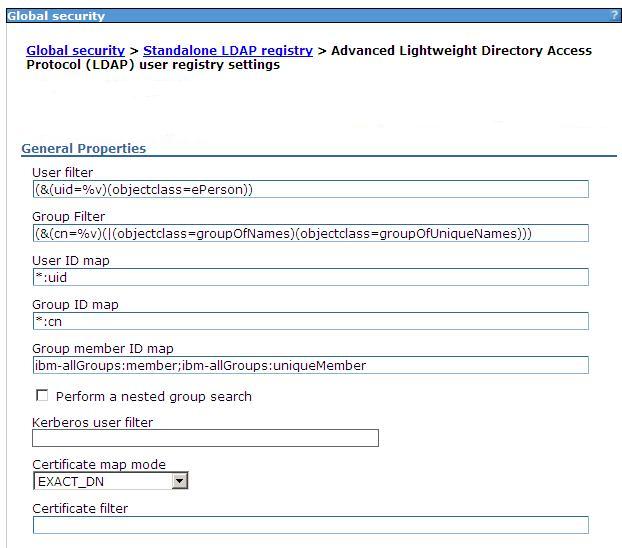
- Under Additional properties, click Advanced LDAP user registry settings .
- Add ;objectCategory:group to the end of the Group member ID map field.
- Click OK and Save to save the changes to the master configuration.
- Stop and restart the admin server so that the changes take effect.
Related concepts
Standalone LDAP registriesLocating a users group memberships in LDAP
Set LDAP user registries
Advanced LDAP user registry settings