Global security settings
Overview
To configure administration and the default application security policy...
-
Security | Global security

This security configuration applies to the security policy for all admin functions and is used as a default security policy for user applications. Security domains can be defined to override and customize the security policies for user applications.
Security has some performance impacts on the applications. The performance impacts can vary depending upon the application workload characteristics. Determine that the needed level of security is enabled for the applications, and then measure the impact of security on the performance of the applications.
When security is configured, validate any changes to the user registry or authentication mechanism panels. Click Apply to validate the user registry settings. An attempt is made to authenticate the server ID or to validate the admin ID (if internalServerID is used) to the configured user registry. Validating the user registry settings after enabling administrative security can avoid problems when you restart the server for the first time.
Settings
- Security configuration wizard
- Launches a wizard that enables you to configure the basic administrative and application security settings. This process restricts admin tasks and applications to authorized users.
Using this wizard, we can...
- Configure application security, resource or J2C security, and a user registry.
- Configure an existing registry
- Enable administrative, application, and resource security.
When you apply changes made by using the security configuration wizard, administrative security is turned on by default.
- Security configuration report
- Launches a security configuration report that displays...
- Core security settings
- Administrative users and groups
- CORBA naming roles
The report does not display info on...
- application level security
- JMS security
- bus security
- Web Services security
When multiple security domains are configured, the report displays the security configuration associated with each domain.
- Enable administrative security
- Administrative security requires users to authenticate before obtaining admin control of the appserver.
When enabling security, set the authentication mechanism configuration and specify a valid user ID and password (or a valid admin ID when internalServerID feature is used) in the selected registry configuration.
The user ID, or admin ID, identifies administrators who manage the environment.
The server ID is used for server-to-server communication.
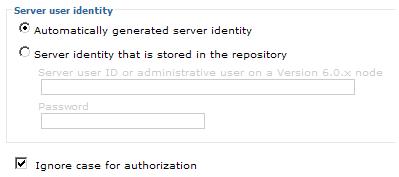
We do not need to enter a server ID and password for internal server ID features. However, optionally, we can specify a server ID and password. Go to...
-
Security | Global security | User account repository | repository | Configure

...and specify the server ID and password in the Server user identity section.
If the server does not start after enabling security within the security domain, or for other problems, resynchronize all files from the cell to nodes. From the node...
-
syncNode -username my_userid -password my_password
- Enable application security
- Provides application isolation and requirements for authenticating application users
In previous releases of WAS, when a user enabled global security, both admin and application security were enabled. In WAS V6.1, the previous notion of global security is split into administrative security and application security, each of which we can enable separately.
Administrative security is enabled, by default. Application security is disabled, by default.
Application security is in effect only when administrative security is enabled.
- Use Java 2 security to restrict application access to local resources
- By default, access to local resources is not restricted. We can choose to disable Java 2 security, even when application security is enabled.
When enabled, if an application requires more Java 2 security permissions than are granted in the default policy, the application might fail to run properly until the required permissions are granted in either app.policy or was.policy of the application. AccessControl exceptions are generated by applications that do not have all the required permissions.
Default: Disabled - Warn if applications are granted custom permissions
- Specifies that during application deployment and application start, the security runtime issues a warning if applications are granted any custom permissions. Custom permissions are permissions defined by the user applications, not Java API permissions. Java API permissions are permissions in the java.* and javax.* packages.
The appserver provides support for policy file management. A number of policy files are available in this product, some of them are static and some of them are dynamic. Dynamic policy is a template of permissions for a particular type of resource. No code base is defined and no relative code base is used in the dynamic policy template. The real code base is dynamically created from the configuration and run-time data. The filter.policy file contains a list of permissions that you do not want an application to have according to the J2EE 1.4 specification.
See on permissions, see the related link about Java 2 security policy files.
We cannot enable this option without enabling the Use Java 2 security to restrict application access to local resources option.
Default: Disabled - Restrict access to resource authentication data
- Enable this option to restrict application access to sensitive Java Connector Architecture (JCA) mapping authentication data.
Consider enabling this option when both of the following conditions are true:
- Java 2 security is enforced.
- The application code is granted the accessRuntimeClasses WebSphereRuntimePermission permission in was.policy found within the application EAR file. For example, the application code is granted the permission when the following line is found in was.policy:
permission com.ibm.websphere.security.WebSphereRuntimePermission "accessRuntimeClasses";
The Restrict access to resource authentication data option adds fine-grained Java 2 security permission checking to the default principal mapping of the WSPrincipalMappingLoginModule implementation. You must grant explicit permission to J2EE applications that use the WSPrincipalMappingLoginModule implementation directly in the (JAAS) login when Use Java 2 security to restrict application access to local resources and the Restrict access to resource authentication data options are enabled.
Default: Disabled - Current realm definition
- Current setting for the active user repository.
This field is read-only.
- Available realm definitions
- Available user account repositories.
The selections appear in a drop-down list containing:
- Local operating system
- Standalone LDAP registry
- Standalone custom registry
- Set as current
- Enables the user repository after it is configured.
Configure settings for one of the following user repositories:
- Federated repositories
- Specify this setting to manage profiles in multiple repositories under a single realm. The realm can consist of identities in:
- The file-based repository that is built into the system
- One or more external repositories
- Both the built-in, file-based repository and in one or more external repositories
Only a user with administrator privileges can view the federated repositories configuration.
- Local operating system
- You cannot use localOS in multi-node or when running as non-root on a UNIX platform.
The local operating system registry is valid only when you use a domain controller or the ND cell resides on a single machine. In the later case, we cannot spread multiple nodes in a cell across multiple machines as this configuration, using the local OS user registry, is not valid.
- Standalone LDAP registry
- Specify this setting to use standalone LDAP registry settings when users and groups reside in an external LDAP directory. When security is enabled and any of these properties change, go to the Security > Global security panel and click Apply or OK to validate the changes.
Since multiple LDAP servers are supported, this setting does not imply one LDAP registry.
- Standalone custom registry
- Specify this setting to implement our own standalone custom registry that implements the com.ibm.websphere.security.UserRegistry interface. When security is enabled and any of these properties change, go to the Global security panel and click Apply or OK to validate the changes.
Default: Disabled - Configure...
- Select to configure the global security settings.
- Web and SIP security
- Under Authentication, expand Web and SIP security to view links to:
- General settings
- Single sign-on (SSO)
- SPNEGO web authentication
- Trust association
- General settings
- Select to specify the settings for Web authentication.
- Single sign-on (SSO)
- Select to specify the configuration values for SSO.
With SSO support, Web users can authenticate once when accessing both WAS resources, such as HTML, JSPs, servlets, enterprise beans, and Lotus Domino resources.
- SPNEGO web authentication
- SPNEGO provides a way for Web clients and the server to negotiate the web authentication protocol used to permit communications.
- Trust association
- Select to specify the settings for the trust association. Trust association is used to connect reversed proxy servers to the appservers.
Use the global security settings or customize the settings for a domain.
The use of trust association interceptors (TAIs) for SPNEGO authentication is now deprecated. The SPNEGO web authentication panels now provide a much easier way to configure SPNEGO.
- RMI/IIOP security
- Under Authentication, expand RMI/IIOP security to view links to:
- CSIv2 inbound communications
- CSIv2 outbound communications
- CSIv2 inbound communications
- Select to specify authentication settings for requests that are received and transport settings for connections that are accepted by this server using the Object Management Group (OMG) Common Secure Interoperability (CSI) authentication protocol.
Authentication features include three layers of authentication that we can use simultaneously:
- CSIv2 attribute layer. The attribute layer might contain an identity token, which is an identity from an upstream server that already is authenticated. The identity layer has the highest priority, followed by the message layer, and then the transport layer. If a client sends all three, only the identity layer is used. The only way to use the SSL client certificate as the identity is if it is the only information that is presented during the request. The client picks up the interoperable object reference (IOR) from the namespace and reads the values from the tagged component to determine what the server needs for security.
- CSIv2 transport layer. The transport layer, which is the lowest layer, might contain an SSL client certificate as the identity.
- CSIv2 message layer. The message layer might contain a user ID and password or an authenticated token with an expiration.
- CSIv2 outbound communications
- Select to specify authentication settings for requests that are sent and transport settings for connections that are initiated by the server using the Object Management Group (OMG) Common Secure Interoperability (CSI) authentication protocol.
Authentication features include three layers of authentication that we can use simultaneously:
- CSIv2 attribute layer. The attribute layer might contain an identity token, which is an identity from an upstream server that already is authenticated. The identity layer has the highest priority, followed by the message layer, and then the transport layer. If a client sends all three, only the identity layer is used. The only way to use the SSL client certificate as the identity is if it is the only information that is presented during the request. The client picks up the interoperable object reference (IOR) from the namespace and reads the values from the tagged component to determine what the server needs for security.
- CSIv2 transport layer. The transport layer, which is the lowest layer, might contain an SSL client certificate as the identity.
- CSIv2 message layer. The message layer might contain a user ID and password or an authenticated token with an expiration.
- Java authentication and authorization service
- Under Authentication, expand Java authentication and authorization service to view links to:
- Application logins
- System logins
- J2C authentication data
- Application logins
- Select to define login configurations that are used by JAAS.
Do not remove the ClientContainer, DefaultPrincipalMapping, and WSLogin login configurations because other applications might use them. If these configurations are removed, other applications might fail.
- System logins
- Select to define the JAAS login configurations that are used by system resources, including the authentication mechanism, principal mapping, and credential mapping.
- J2C authentication data
- Select to specify the settings for the JAAS J2C authentication data.
Use the global security settings or customize the settings for a domain.
- LTPA
- Select to encrypt authentication information so that the application server can send the data from one server to another in a secure manner.
The encryption of authentication information that is exchanged between servers involves the LTPA mechanism.
- Kerberos and LTPA
- Select to encrypt authentication information so that the application server can send the data from one server to another in a secure manner.
The encryption of authentication information that is exchanged between servers involves the Kerberos mechanism.
Kerberos must be configured before this option can be selected.
- Kerberos configuration
- Select to encrypt authentication information so that the application server can send data from one server to anther in a secure manner.
The encryption of the authentication information that is exchanged between servers involves the KRB5 of LTPA mechanism.
- Authentication cache settings
- Select to set the authentication cache settings.
- Use realm-qualified user names
- Specifies that user names that are returned by methods, such as the getUserPrincipal() method, are qualified with the security realm in which they reside.
- Security domains
- Use the Security Domain link to configure additional security configurations for user applications.
For example, if we want use a different user registry for a set of user applications than the one used at the global level, we can create a security configuration with that user registry and associate it with that set of applications. These additional security configurations can be associated with various scopes (cell, clusters/servers, SIBuses). Once the security configurations have been associated with a scope all of the user applications in that scope use this security configuration. Read about Multiple security domains for more detailed information.
For each security attribute, we can use the global security settings or customize settings for the domain.
- External authorization providers
- Select to specify whether to use the default authorization configuration or an external authorization provider.
The external providers must be based on the Java uthorization Contract for Containers (JACC) spec to handle the Java (TM) 2 Platform, Enterprise Edition (J2EE) authorization. Do not modify any settings on the authorization provider panels unless we have configured an external security provider as a JACC authorization provider.
- Custom properties
- Select to specify name-value pairs of data, where the name is a property key and the value is a string.
Related concepts
Java 2 security
Multiple security domains
Related tasks
Secure specific appservers
Enable security
Set FIPS JSSE files
Set multiple security domains
Related
RSA token authentication settings
Authentication mechanisms and expiration
Local operating system settings
Standalone LDAP registry settings
Standalone custom registry settings
Administrative roles
Directory conventions
Java 2 security policy files
Set security domains
Related information
Cryptographic Module Validation Program FIPS 140-1 and FIPS 140-2 Pre-validation List