Configure programmatic logins for JAAS
A new JAAS login configuration can be added and modified using the console. The changes are saved in the cell-level security document and are available to all managed appservers.
JAAS is a collection of WAS strategic authentication APIs and replaces the CORBA programmatic login APIs. WAS provides some extensions to JAAS:
- com.ibm.websphere.security.auth.WSSubject.
Extends the JAAS authorization model to J2EE resources.
You can configure the JAAS login in the console and store this login configuration in the Application Server configuration. However, WAS still supports the default JAAS login configuration format (plain text file) that is provided by the JAAS default implementation.
If duplicate login configurations are defined in both the WAS configuration API and the plain text file format, the one in the WAS configuration API takes precedence. Advantages to defining the login configuration in the WebSphere configuration API include:
- User interface support in defining JAAS login configuration
- Central management of the JAAS login configuration
- Distribution of the JAAS login configuration during installation
Due to a design oversight in JAAS V1.0, the javax.security.auth.Subject.getSubject method does not return the subject that is associated with the running thread inside a java.security.AccessController.doPrivileged code block. This problem presents an inconsistent behavior that might cause unfavorable results. The com.ibm.websphere.security.auth.WSSubject API provides a workaround to associate the subject to a running thread.
- User interface support in defining JAAS login configuration
- Proxy LoginModule.
Loads the actual LoginModule module. The default JAAS implementation does not use the thread context class loader to load classes. The LoginModule module cannot load if the LoginModule class file is not in the application class loader or the Java extension class loader class path. Due to this class loader visibility problem, WAS provides a proxy LoginModule module to load the JAAS LoginModule using the thread context class loader.
You do not need to place the LoginModule implementation on the application class loader or the class path for the Java extension class loader with this proxy LoginModule module.
If you do not want to use the Proxy LoginModule module, you can place the LoginModule module in...
app_server_root/lib/ext/
However, this action is not recommended due to the security risks.
JAAS login configurations are defined in the WAS configuration API security document. Click...
Security | Secure administration, applications, and infrastructure | Java Authentication and Authorization Service | Application logins
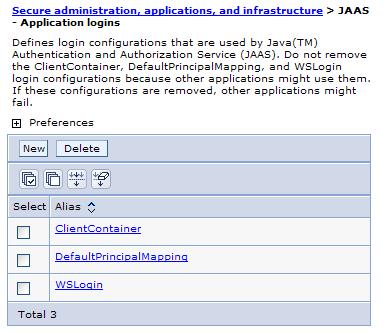
The following JAAS login configurations are available:
- ClientContainer
- Defines a login configuration and a LoginModule implementation that is similar to that of the WSLogin configuration, but enforces the requirements of the WAS client container.
- DefaultPrincipalMapping,
- Defines a special LoginModule module that is typically used by J2EE connectors to map an authenticated WAS user identity to a set of user authentication data (user ID and password) for the specified back-end enterprise information system. For more information about J2EE Connector and the DefaultMappingModule module, refer to the J2EE security section.
- WSLogin
- Defines a login configuration and a LoginModule implementation that applications can use in general.
A new JAAS login configuration can be added and modified using the console. The changes are saved in the cell-level security document and are available to all managed appservers. An appserver restart is required for the changes to take effect at run time.
Do not remove or delete the predefined JAAS login configurations (such as, ClientContainer, WSLogin, and DefaultPrincipalMapping). Deleting or removing them can cause other enterprise applications to fail.
Procedure
- Delete a JAAS login configuration.
- Click...
Security | Secure administration, applications, and infrastructure | Java Authentication and Authorization Service | Application logins
The Application Login Configuration panel is displayed.
- Select the check box for the login configurations to delete and click Delete.
- Click...
- Create a new JAAS login configuration.
- Click...
Security | Secure administration, applications, and infrastructure | Java Authentication and Authorization Service | Application logins | New
The Application Login Configuration panel is displayed.
- Specify the alias name of the new JAAS login configuration and click Apply. This value is the name of the login configuration that you pass in the javax.security.auth.login.LoginContext implementation for creating a new LoginContext context.
Click Apply to save changes and to add the extra node name that precedes the original alias name. Clicking OK does not save the new changes in the security.xml file.
- Under Additional properties, click JAAS Login Modules.
- Click New.
- Specify the Module class name. Specify the WAS proxy LoginModule module because of the limitation of the class loader visibility.
- Specify the LoginModule implementation as the delegate property of the Proxy LoginModule module. The WAS proxy LoginModule class name is...
com.ibm.ws.security.common.auth.module.proxy.WSLoginModuleProxy
- Select Authentication strategy from the list and click Apply.
- Under Additional properties, click Custom properties.
The Custom properties panel is displayed for the selected LoginModule.
- Create a new property with the name delegate and the value of the real LoginModule implementation. You can specify other properties like debug with the true value. These properties are passed to the LoginModule class as options to the initialize method of the LoginModule instance.
- Click Save.
For a ND installation, make sure that a file synchronization operation is performed to propagate the changes to other nodes.
Several locations are within the WAS directory structure where you can place a JAAS login module. The following list provides locations for the JAAS login module in order of recommendation:
- Within an enterprise archive (EAR) file for a specific J2EE application.
If you place the login module within the EAR file, the login module is accessible by the specific application only.
- In the WAS-shared library.
If you place the login module in the shared library, specify which applications can access the module.
- In the Java extensions directory.
If you place the JAAS login module in the Java extensions directory, the login module is available to all applications.
Although the Java extensions directory provides the greatest availability for the login module, place the login module in an application EAR file. If other applications need to access the same login module, consider using shared libraries.
- Click...
- Change the plain text file.
WAS supports the default JAAS login configuration format, which is a plain text file, that is provided by the JAAS default implementation. However, a tool is not provided that edits plain text files in this format. You can define the JAAS login configuration in the plain text file...
app_server_root/properties/wsjaas.conf
Any syntax errors can cause the incorrect parsing of the plain JAAS login configuration text file. This problem can cause other applications to fail. Java client programs that use JAAS for authentication must invoke with the JAAS configuration file specified. This configuration file is set in...
the app_server_root/bin/launchClient.bat
...file as...
set JAAS_LOGIN_CONFIG=-Djava.security.auth.login.config=%install_root%\properties\wsjaas_client.conf
If the launchClient.bat file is not used to invoke the Java client program, verify that the appropriate JAAS configuration file is passed to the Java virtual machine with the -Djava.security.auth.login.config flag.
Results
A new JAAS login configuration is created or an old JAAS login configuration is removed. An enterprise application can use a newly created JAAS login configuration without restarting the application server process.However, new JAAS login configurations that are defined in the app_server_root/properties/wsjaas.conf file, do not refresh automatically. Restart the appservers to validate changes. These JAAS login configurations are specific to a particular node and are not available for other appservers running on other nodes.
What to do next
Create new JAAS login configurations that are used by enterprise applications to perform custom authentication. Use these newly defined JAAS login configurations to perform programmatic login.Login configuration for Java Authentication and Authorization Service
Configuration entry settings for Java Authentication and Authorization Service
System login configuration entry settings for Java Authentication and Authorization Service
Login module settings for Java Authentication and Authorization Service
Login module order settings for Java Authentication and Authorization Service
Login configuration settings for Java Authentication and Authorization Service
Manage J2EE Connector Architecture authentication data entries
Related concepts
J2EE connector security
Programmatic login
Related tasks
Developing programmatic logins with the Java Authentication and Authorization Service
Manage shared libraries
Customizing application login with Java Authentication and Authorization Service