Manage policy sets and bindings for service providers at the application level using the administrative console
Use this administrative console task to manage policy sets for an application or its services, endpoints, and operations.
Before completing this task, we need to install one or more JAX-WS and attach a policy set to each web service.
We have developed a web service containing all the necessary artifacts and deployed the web services application into the application server instance. Now, we can attach or detach policy sets and manage the associated bindings.
The policy set information is displayed in the Attached Policy Set column. If a policy set is directly attached, then the policy set name appears; for example, WS-I RSP is displayed. If there is no policy set attached, and a policy set is attached at a higher level, then the word inherited in parentheses is appended to the policy set name: WS-I RSP (inherited). If there is no policy set attached directly or at a higher level, then None is displayed.
Every attachment of a policy set to a service artifact has an assigned binding. The binding information is displayed in the Binding column. The Binding column can contain the following values:
- Not applicable. There is no policy set attached, either directly or to a higher level service resource.
- Binding_name or Default. The binding name is displayed if a policy set is attached directly and an application-specific binding or a general binding is assigned, for example, MyBindings1. Default is displayed if a policy set is attached directly but the service resource uses the default bindings.
- Binding_name (inherited) or Default (inherited). A service resource inherits the bindings from an attachment to a higher level resource.
In v7.0 and later, there are two types of bindings, application specific bindings and general bindings.
Application specific binding
Create application specific bindings only at a policy set attachment point. These bindings are specific to and constrained to the characteristics of the defined policy. Application specific bindings are capable of providing configuration for advanced policy requirements, such as multiple signatures; however, these bindings are only reusable within an application. Furthermore, application specific bindings have very limited reuse across policy sets.
When creating an application specific binding for a policy set attachment, the binding begins in a completely unconfigured state. We must add each policy, such as WS-Security or HTTP transport, to override the default binding and fully configure the bindings for each policy that we have added. For WS-Security policy, some high level configuration attributes such as TokenConsumer, TokenGenerator, SigningInfo, or EncryptionInfo might be obtained from the default bindings if they are not configured in the application specific bindings.
For service providers, we can only create application specific bindings by selecting Assign Binding > New Application Specific Binding for service provider resources that have an attached policy set. See service providers policy sets and bindings collection. Similarly, for service clients, we can only create application specific bindings by selecting Assign Binding > New Application Specific Binding for service client resources that have an attached policy set. See service client policy set and bindings collection.

General bindings
General bindings were introduced in v7.0. These bindings can be configured to be used across a range of policy sets and can be reused across applications and for trust service attachments. Though general bindings are highly reusable, they are however not able to provide configuration for advanced policy requirements, such as multiple signatures. There are two types of general bindings:
- General provider policy set bindings
- General client policy set bindings
Create general policy set bindings by copying an existing binding or by creating a new one. For WS-Security bindings, copy an existing sample binding. Creating a new policy set binding from scratch for WS-Security can cause unexpected problems at run time.
To create general provider policy set bindings, in the administrative console, select...
-
Services > Policy sets > General provider policy set bindings > New or Copy
To create general client policy set bindings, select...
-
Services > Policy sets > General client policy set bindings > New or Copy
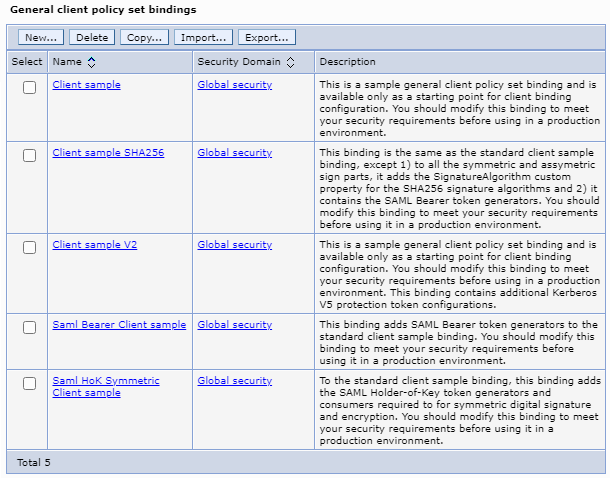
See Define and manage service client or provider bindings. General provider policy set bindings can also be used for trust service attachments.
After we make a copy of the provider or client sample bindings, customize only the settings of our new copy to suit your purposes. Do not remove anything from your binding copy, such as token generators, token consumers, sign parts, or encrypt parts. We can add things to your binding copy if needed, but deleting information can cause unanticipated errors at run time.
Depending on the assigned security role when security is enabled, we might not have access to text entry fields or buttons to create or edit configuration data. Review the administrative roles documentation to learn more about the valid roles for the application server.
Tasks
- Open the administrative console.
- Applications > Application Types >
WebSphere enterprise applications >Service_provider_application_instance > Service provider policy sets and bindings.
[Optional] When we are accessing a business-level application, click Business-level applications (BLA) > My_BLA > BLA_instance > Service provider policy sets and bindings. Alternatively, click Services > Service providers > My_BLA > BLA_instance > Service provider policy sets and bindings.
- Select the check box next to a service resource of interest.
- Click Attach to attach a policy set to an application, service, endpoint or operation.
- [Optional] Click Detach to detach a policy set from a list of attached policy sets for an application, service provider, endpoint or operation.
- Click Assign Binding to select from a list of available bindings for the selected policy set attachment.
All the bindings are listed along with the following options:
Bindings Description Default Default binding for the selected service, endpoint or operation. We can specify client and provider default bindings to be used at the cell level or global security domain level, for a particular server, or for a security domain. The default bindings are used when an application specific binding has not been assigned to the attachment. When we attach a policy set to a service resource, the binding is initially set to the Default. If we do not specifically assign a binding to the attachment point using this Assign Binding action, the default specified at the nearest scope is used. For any policy set attachment, the runtime checks to see if the attachment includes a binding. If so, it uses that binding. If not, the runtime checks in the following order and uses the first available default binding:
- Default general bindings for the server
- Default general bindings for the domain in which the server resides
- Default general bindings for the global security domain
New Application Specific Binding Select this option to create a new application specific binding for the policy set attachments. The new binding we create is used for the selected resources. If we select more than one resource, ensure that all selected resources have the same policy set attached. Provider sample Select this option to use the Provider sample binding. Provider sample V2 Select this option to use the Provider sample V2 binding when we are using either the Kerberos V5 WSSecurity default or the TrustServiceKerberosDefault policy sets. Saml Bearer Provider sample Select this option to use the Saml Bearer Provider sample. The Saml Bearer Provider sample extends the Provider sample binding to support SAML Bearer token usage scenarios. Use this sample with any of the SAML bearer token default policy sets. Saml HoK Symmetric Provider sample Select this option to use the Saml HoK Symmetric Provider sample. The Saml HoK Symmetric Provider sample extends the Provider sample binding to support SAML holder-of-key (HoK) symmetric key token usage scenarios. Use this sample with one of the SAML HoK Symmetric key default policy sets: either SAML11 HoK Symmetric WSSecurity default or SAML20 HoK Symmetric WSSecurity default. - To close the drop down list for the assign binding action, click Assign Binding.
When we finish this task, a policy set is attached or detached, and a binding is assigned to the service artifact.
Example
If we have configured a service provider application instance, app1 and we want, for example, to attach theUsername WSSecurity default policy set to the application, first locate app1 application in the Applications > Application Types > WebSphere enterprise applications. Click app1 > Service provider policy sets and bindings under the Web Services Properties section. Select the check box next to the app1 service application. Click Attach and select Username WSSecurity default policy set. Click Save, to save the changes to the master configuration. We are returned to the Applications > Application Types > WebSphere enterprise applications page.
To assign a binding to the attached policy set, click app1 > Service provider policy sets and bindings. Select the check box next to the app1 service application and click Assign Binding. Select Provider sample binding from the list. Click Save, to save the changes to the master configuration.
What to do next
We can proceed to view service providers at the cell level using the administrative console.
Subtopics
- Service provider policy sets and bindings collection
Attach and detach policy sets to an application, a service provider, its endpoints, or operations. We can select the default bindings, create new application-specific bindings, or use bindings created for an attached policy set. We can view or change whether the service provider can share its current policy configuration.