Auditable security events
Auditable security events are security events that have audit instrumentation added to the security run time code to enable them to be recorded. Event filters are configured to specify which auditable security events are recorded to the audit log files.
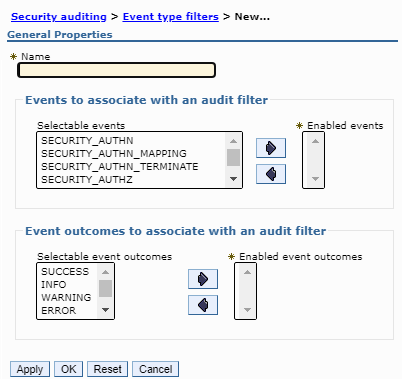
The following list describes each valid auditable event that we can specify as an enabled event type when creating an event filter:
| Event name | Description |
|---|---|
| SECURITY_AUTHN | Audits all authentication events |
| SECURITY_AUTHN_MAPPING | Audits events that record mapping of credentials where two user identities are involved |
| SECURITY_AUTHN_TERMINATE | Audits authentication termination events such as a form-based logout |
| SECURITY_AUTHZ | Audits events related to authorization checks when the system enforces access control policies |
| SECURITY_RUNTIME | Audits runtime events such as the starting and the stopping of security servers. This event type is not meant for administrative operations performed by a system administrator as such operations need to use the other SECURITY_MGMT_* event types. |
| SECURITY_MGMT_AUDIT | Audits events that record operations related to the audit subsystem such as starting audit, stopping audit, turning audit on or off, changing configuration of audit filters or level, archiving audit data, purging audit data, and so on. |
| SECURITY_RESOURCE_ACCESS | Audits events that record all accesses to a resource. Examples are all accesses to a file, all HTTP requests and responses to a given web page, and all accesses to a critical database table |
| SECURITY_SIGNING | Audits events that record signing such as signing operations used to validate parts of a SOAP Message for web services |
| SECURITY_ENCRYPTION | Audits events that record encryption information such as encryption for web services |
| SECURITY_AUTHN_DELEGATION | Audits events that record delegation, including identity assertion, RunAs, and low assertion. Used when the client identity is propagated or when delegation involves the use of a special identity. This event type is also used when switching user identities within a given session. |
| SECURITY_AUTHN_CREDS_MODIFY | Audits events to modify credentials for a given user identity |
| SECURITY_FORM_LOGIN | Audits events of the user being logged in and the remote IP address from which the login is initiated along with the timestamp and the outcome. |
| SECURITY_FORM_LOGOUT | Audits events of the user being logged out and the remote IP address from which the logout is initiated along with the timestamp and the outcome. |
Support for the SECURITY_RUNTIME auditing event type has been fully implemented for this release of WebSphere Application Server. It audits runtime events such as the starting and the stopping of security servers.
(ZOS)
| Event name | SMF Code | SMF Unload Keyword |
|---|---|---|
| SECURITY_AUTHN | 1 | *WASAUTN |
| SECURITY_AUTHN_MAPPING | 3 | *WASAUTM |
| SECURITY_AUTHN_TERMINATE | 2 | *WASAUTT |
| SECURITY_AUTHZ | 4 | *WASAUTZ |
| SECURITY_MGMT_CONFIG | 8 | *WASCONF |
| SECURITY_MGMT_POLICY | 5 | *WASPOLM |
| SECURITY_MGMT_PROVISIONING | 9 | *WASPROV |
| SECURITY_MGMT_RESOURCE | 10 | *WASRESM |
| SECURITY_RUNTIME | 7 | *WASRUNT |
| SECURITY_RUNTIME_KEY | 11 | *WASKEYR |
| SECURITY_MGMT_KEY | 12 | *WASKEYM |
| SECURITY_MGMT_AUDIT | 13 | *WASAUDI |
| SECURITY_MGMT_REGISTRY | 6 | *WASREGM |
| SECURITY_RESOURCE_ACCESS | 14 | *WASACCE |
| SECURITY_SIGNING | 15 | *WASSIGN |
| SECURITY_ENCRYPTION | 16 | *WASCRYP |
| SECURITY_AUTHN_DELEGATION | 17 | *WASDELE |
| Event Outcome | SMF Qualifier | SMF Unload Keyword |
|---|---|---|
| SUCCESSFUL | 0 | SUCCESS |
| INFO | 1 | INFO |
| WARNING | 2 | WARNING |
| FAILURE | 3 | FAILURE |
| REDIRECT | 4 | REDIRECT |
| DENIED | 5 | DENIED |
To provide support for federal regulation compliance with minimal performance usage, support is added to allow for the capture of Web UI logins and logouts with a minimum amount of audit data.
The following properties, supported in the audit.xml file, are introduced:
- com.ibm.audit.terse.form.login, with a value that consists of a space-delimited list of valid outcomes.
- com.ibm.audit.terse.form.logout, with a value that consists of a space-delimited list of valid outcomes.
- com.ibm.audit.terse.form login enables the SECURITY_FORM_LOGIN event with the outcomes specified in "value".
- com.ibm.audit.terse.form.logout enables the SECURITY_FORM_LOGOUT event with the outcomes specified. in "value".
The resulting audit event contains only: the time stamp, the user being logged in (or out), the remote IP address from which the login or logout is initiated, and the outcome.
Example audit.xml file
<?xml version="1.0" encoding="UTF-8"?>
<security:Audit xmi:version="2.0"
xmlns:xmi="http://www.omg.org/XMI"
xmlns:security="http://www.ibm.com/websphere/appserver/schemas/5.0/security.xmi"
xmi:id="Audit_1173199825578">
<auditSpecifications xmi:id="AuditSpecification_1173199825610" enabled="true" name="DefaultAuditSpecification_3">
<event>SECURITY_AUTHN_TERMINATE</event>
<outcome>SUCCESS</outcome>
<outcome>REDIRECT</outcome>
<outcome>FAILURE</outcome>
</auditSpecifications>
<auditPolicy xmi:id="AuditPolicy_1173199825608"
auditEnabled="true"
auditorId="sadie"
auditorPwd="{xor}"
sign="false"
encrypt="false"
batching="false"
verbose="false">
<auditEventFactories xmi:id="AuditEventFactory_1173199825608"
name="auditEventFactoryImpl_1"
className="com.ibm.ws.security.audit.AuditEventFactoryImpl"
auditServiceProvider="AuditServiceProvider_1173199825608"
auditSpecifications="AuditSpecification_1173199825610"/>
<auditServiceProviders xmi:id="AuditServiceProvider_1173199825608"
name="auditServiceProviderImpl_1"
className="com.ibm.ws.security.audit.BinaryEmitterImpl"
eventFormatterClass=""
maxFileSize="10" maxLogs="100"
fileLocation="$(LOG_ROOT)"
auditSpecifications="AuditSpecification_1173199825610"/>
<properties xmi:id="Property_1"
name="com.ibm.audit.terse.form.login"
value="SUCCESS FAILURE"
description="dtcc custom property"/>
<properties xmi:id="Property_2"
name="com.ibm.audit.terse.form.logout"
value="SUCCESS FAILURE ERROR"
description="dtcc custom property"/>
</auditPolicy>
</security:Audit>
Property_1 defines that we will be capturing the terse SECURITY_FORM_LOGIN event type and an audit event will only be captured for outcomes of either success or failure.
Property_2 defines that we will be capturing the terse SECURITY_FORM_LOGOUT event type and an audit event will only be captures if the outcome is success, failure or error.
Starting with WAS V9, support is added to be able to configure the SECURITY_FORM_LOGIN and SECURITY_FORM_LOGOUT auditevent types either through the administrative console, or through wsadmin scripting. Specifying the properties is still supported, and if specified, there is not a need to reconfigure using the administrative console or wsadmin scripting.