Manage certificate expiration settings
To configure the certificate expiration monitor.
-
Security | SSL certificate and key management | Configuration settings | Manage certificate expiration
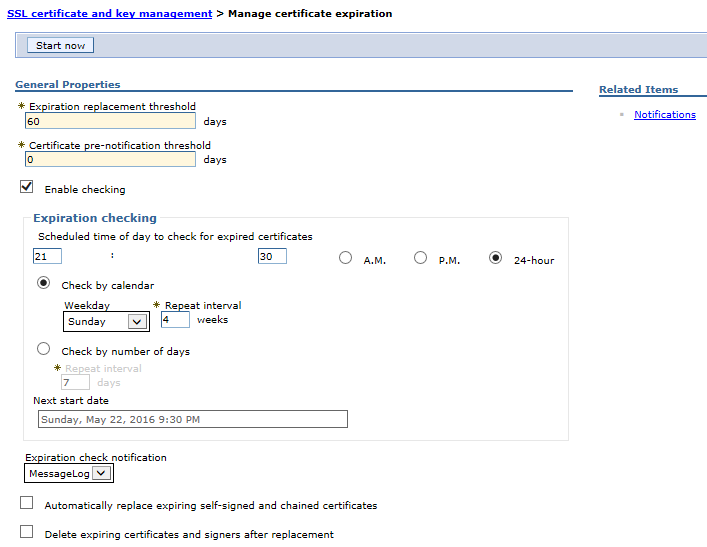
To see the changes to the Expiration checking fields, click Apply.
| Start now | Start certificate monitoring. When the monitor runs, it visits all the key stores and checks to see if they are within certificate expiration range. If we set the option to delete or replace expired certificates, we can run these operations immediately by pressing Start now. | ||||||
| Expiration notification threshold | Period of time that occurs chronologically just before the expiration day of the certificate, within which, if the ExpirationMonitor thread runs, and Automatically replace expiring self-signed and chained certificates is enabled, a new self-signed or chained certificate is generated. By default, the replacement period for the certificate is 60 days in length or less as defined in the daysBeforeNotification property.
Avoid trouble: Enabling WAS to automatically replace the expiring certificates in a production environment can potentially cause a short- or long-term outage. IBM recommends instead changing certificates manually. There is a pre-notification period where the certificate is added to the notification list but not touched for 90 days prior to the 60 days. By default, this pre-notification period is 90 days in length as defined in the com.ibm.ws.security.expirationMonitorNotificationPeriod property.
| ||||||
| Enable checking | Certificate monitor is active and will run as scheduled. | ||||||
| Scheduled time of day to check for expired certificates | Scheduled time that the system checks for expired certificates. We can type the scheduled time in hours and minutes, specify either A.M. or P.M., or 24-hour.
| ||||||
| Check by calendar | Schedule a specific day of the week on which the expiration monitor runs. For example, it might run on Sunday.
| ||||||
| Weekday | Day of the week on which the expiration monitor runs if Check on a specific day is selected.
| ||||||
| Repeat interval | Period of time between each schedule time to check for expired certificates or the interval between schedule
checks.
| ||||||
| Check by number of days | Schedule a specific number of days between each run of the expiration monitor. The day of the week on which this occurs is not counted. For example, if set the interval to check for expired certificates every seven days, the expiration monitor runs on day eight.
| ||||||
| Next start date | Date for the next scheduled check. This allows the deployment manager to be stopped and restarted without resetting the date. | ||||||
| Expiration check notification | Notification type (either email, or an entry in the system log) when an expiration monitor runs.
| ||||||
| Automatically replace expiring self-signed certificates and chained certificates | New self-signed certificate or chained certificate be generated using the same certificate information if the expiration notification threshold is reached. The old certificate is replaced and uses the same alias. All old signers are managed by the key store configuration are also replaced. The system only replaces self-signed certificates.
This checkbox is only applicable when using file based keystores.
| ||||||
| Delete expiring certificates and signers after replacement | Whether to completely remove old, self-signed
certificates from the key store during a replace operation or leave
them there under a renamed alias. If an old certificate is not deleted, the system renames the alias so that the new certificate can use the old alias, which might be referenced elsewhere in the configuration.
This checkbox is only applicable when using file based keystores.
|
Related
SSL certificate and key management